Email is a ubiquitous tool in modern life, yet few fully utilise its power, or understand its dangers.
This article is a definitive guide to the power and options available for email use both in business and your personal life. I’ll be discussing important privacy considerations, hosting options, device and configuration options and email domain naming.
By the end of this article, you will probably be keen to buy your own domain name, and employ a lot of these strategies. Some require a lot of technical know-how.
Dygiphy can setup and implement everything that’s discussed in this article, so please contact us to find out more.
Privacy – the stuff you need to know
A unique identifier
Have you ever wondered why most websites ask you to register with your email address? It’s because that single piece of information can uniquely identify you in the world. Unlike your name or birthdate, your email address is unique.
Once a company has that address, they don’t just use it to contact you, they frequently cross reference it against other sites and institutions to which you have also provided your email address. They can (and do) share and sell your details to other companies, and specialist companies aggregate it and build up detailed profiles about who you are and what you do.
Have you ever used that “Login with Facebook” option? Ever wondered why it’s there? Sure it’s convenient, but it also lets Facebook cross reference the data from every site you use it with, and against the email account you use with Facebook. TIP: never, ever (ever) use login with Facebook if you value your privacy.
Those details are a valuable commodity. There’s a reason why each site asks for so much information – most of which is not necessary for providing the service you are signing up for. Your email address is the main key that enables it all to be cross referenced.
But don’t worry, there’s a solution. Read on.
Email is insecure
Did you know that nearly all email is un-encrypted? The reason is fairly simple. If you were to encrypt an email before sending it to someone you didn’t know – how would they de-crypt it? They don’t have the password.
More modern forms of communication (WhatsApp is a good example) use a highly secure form of public and private key encryption that enables them to transmit your message securely from end to end. They can do this because they control the sending and receiving software, and everything in-between.
Unfortunately, the same is not true for email.
You can configure your email client to transmit your email securely to your email provider (and this is good practice), but once it gets there it’s not encrypted any more. Also you have no control over how it is then transferred to the recipient who may be using completely different software and email providers.
Also, ISP and email hosts may be able to access and read these emails in your mailbox if the email account is hosted with them. Third party providers (Gmail, Hotmail, Yahoo, etc) can’t because your email account is encrypted using your password – although if you are sending your email using an un-encrypted protocol, that data can be intercepted and read before it reaches your provider.
A little later I’ll talk about some options that are more secure.
Your email address
It used to be that you’d have to change your email address when you changed your ISP. With Bigpond, iinet, Westnet or any provider, changing to a new ISP meant changing your email account. This was such a hassle it locked many into the same ISP, even if you were keen to change.
Then along came the free third party providers (Gmail, Hotmail, Yahoo, etc). You could open an account with them and freely move between ISPs without changing your email. It liberated us from our ISP.
But this doesn’t solve the privacy issue – it makes it worse. Now that you never change your email address, it is used everywhere. And occasionally, the services that are storing those details get hacked.
Spam
The longer you use the same email address, the more spam it attracts. Spam filters do their bit, but it gets to the point where there is so much spam in your account, you find it hard to find the real email. Once a site with your details gets hacked, there can be an explosion of spam as well.
This happened to me a few years ago when Adobe’s systems were hacked, and the email address I had used to register was suddenly swamped by spam. Lucky for me, I had the following strategy in place.
Buy your own Domain Name
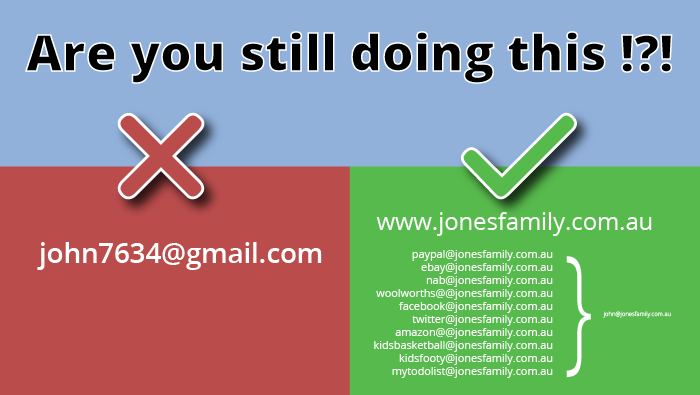
If you are a business, owning your own domain makes perfect sense. But why would you want one for personal use?
When you own a domain name, you also own every email address that can be sent to it. You can literally make up any email address you like and control where it get’s delivered.
Why would you want to do this? Here’s an example.
Create your own email address
Let’s say you own jonesfamily.com.au. You could create the following email addresses:
- facebook1@jonesfamily.com.au
- paypal@jonesfamily.com.au
- amazon@jonesfamily.com.au
- anz@jonesfamily.com.au
- woolworths@jonesfamily.com.au
If you create the above, you can use each to register with those companies. And because they are all different, those companies can’t cross reference your data to build a profile. Also, if one of the addresses starts getting too much spam, you can just change it. Your paypal@jonesfamily.com.au could become paypal1@jonesfamily.com.au for example.
But hang on, you’re probably thinking it will be a major pain to setup and check all these email accounts. The good news is you don’t have to.
The power of the Email Catchall
When you configure email accounts for a domain name, you can can setup email accounts and catchalls (yes literally catch-all emails). This is what they do.
Email Accounts
An email account is a mailbox into which email is delivered. The email is stored in the account, and can be access via browsers, devices and email clients (more on this later).
An email account has only one email address. Anything that is delivered to that address is stored in the account until it is retrieved by the owner.
Continuing our Jones Family theme, let’s say we create the account kevin@jonesfamily.com.au,. This is the account Kevin uses with family and friends. It’s his secret account, and he doesn’t give it to any other website he registers with. Instead, he creates new ones as discussed above.
Catchalls
So what happens to email that goes to an address at jonesfamily.com.au that doesn’t have a corresponding email account? By default, it will get bounced by the mail server, and the sender will get an error message that the mail was undeliverable.
That is unless a catchall was setup to literally catch-all emails. A catchall tells the mail server to collect up all other email to the jonesfamily.com.au domain and send it somewhere. We are going to send it to kevin@jonesfamily.com.au.
Now Kevin can create any email address he wants using his domain, and the mail server will catch it and send it to his secret email account. When it arrives in his email box, it will still have the original address it was sent to.
Kevin doesn’t have to configure or setup anything each time he creates an email address. He just makes it up, and the catchall will do the rest.
This provides a massive security benefit that cannot be overstated. If Kevin gets an email sent to paypal@jonesfamily.com.au, he knows that it should only be coming from Paypal. Equally, if he receives an email pretending to be from Paypal, but it wasn’t sent to his paypal address, he’ll know it’s a phishing (ph-fishing for your details) email and should be ignored. He’ll also discover (as I frequently do) that companies are selling (or have been hacked) his details, when unrelated emails are delivered to an account he knows should only be used by one company.
And don’t worry, If one of the addresses gets overrun by spam, he can block it (either with his client, or with the email server).
POP, IMAP and Webmail
These are terms you may have encountered when setting up your email on your device or PC. These are not different types of email accounts, but are different ways of retrieving email from an account.
POP
POP (post office protocol) is a way the email program on your device or desktop accesses the contents of your email account stored on a remote server.
When you retrieve email using POP, it will make a copy of the email and store it on your PC or device. If the email account is then deleted or inaccessible, you can still access the local copy of the email.
POP is the most commonly used protocol, partly because it was a way to access email offline in the days when internet access was less accessible.
When configuring with POP, you can tell your email client to delete the copy of the email on the server, either immediately, or after a period of time (normally 14 days). This helps prevent the email account filling up.
If more than one device is configured to access the same email account, it will be able to download a duplicate copy of the same email as long as the first device to access it did not delete it first. This is the main reason to configure POP with 14 day deletion.
Because all email accounts have a storage quota, POP is an easy way to make sure your email is removed from the server automatically, synchronise mail across devices, and keep a local copy that you can access forever.
IMAP
Alternatively, you can configure your email clients with IMAP (Internet Message Access Protocol).
IMAP does not make a copy of your email. When your device connects to the email account, it just reads it directly and leaves it on the server.
IMAP can also store a copy of email that you send from your devices back into the Sent folder of your email account, and allows you to create sub folders into which you can organise your email. Because everything is kept in the email account, any other IMAP device that connects to it will see the same content.
In many ways, IMAP works just like a storage cloud.
The downside to IMAP is that it never deletes email from the server, which means it will constantly fill up, and eventually exceed your storage quota. When this happens, you need to manually move or delete individual emails (unless you were organised enough to do this when they arrived).
Because IMAP does not create a copy of your email, you cannot always access it when you are offline (it depends on your email program). Also, when you delete the email, it’s gone for good on every device that used IMAP to access it.
If you want to keep a copy of your email and your email account is full, you can move the email to local folders on your device, if the client supports that feature.
In general at dygiphy, we advise against the use of IMAP due to the issue of quotas, and the risk of losing emails that did not automatically backup a copy to local storage.
Webmail
In many ways, web mail is the same as IMAP, only you are using a web based email client to access your account. Webmail has all the same pros and cons of IMAP, except that you don’t have the ability to download your email to your PC or device.
Webmail is great in combination with one of the above (particularly POP). If you are on holidays and have access to a browser, you can check your email even when you can’t connect your PC or device to the internet. But once you can, that email will still be there available for download.
Hosting Options
Hosting is a service provided by the companies that operate the file servers and computers on which your email account is stored. There are 4 main types, and it’s good to know what each are good at. You may discover you are using the wrong type for your needs.
ISPs
ISPs (internet service providers) are the companies that provide your internet connection. Nearly all of them provide an email service.
Mostly they are a very limited service with small quotas and limited features. If you decide to change ISP, you will not be able to take your email address with you.
In general, I don’t advise the use of ISP based email.
Third Party Hosts
These are companies like Gmail, Hotmail and Yahoo. They offer better quotas, more features and greater security. They are also mostly free.
The downside (as with ISPs) is that you can’t use your own domain name. You have to use the domain name of the provider (ie @gmail.com, @bigpond.com, @hotmail.com).
Setting up and managing multiple accounts is time-consuming, complex to access and not very configurable.
Web Hosted Email
Also sometimes called cPanel email, this is a service that comes with website hosting. This is the type of email we provide at dygiphy by default when we are providing websites to companies, and it suits most client’s needs.
With web hosting, we can configure multiples domains, email accounts, catchalls, forwards, etc. You name it – it can be done.
Web hosted email shares the same server space as your website, and therefore the same quota. We offer quotas of between 5 and 100gb, which suits just about every small business, charity or community group – especially when combined with POP access.
You don’t have to have a website to have a domain hosted email account. Anyone can choose this option for business or personal use, however it requires a lot of technical experience to setup.
Contact us at dygiphy if you’d like to explore this option further.
Exchange Server (Microsoft 365)
Exchange Server is a set of technologies provided by Microsoft and has been the email solution of choice for large businesses for decades.
Until recently, to run an exchange server you really needed an entire technology department in-house. It wasn’t really an option for smaller businesses.
Recently however, Microsoft has offered their exchange server technology as a cloud based service. This makes it an option for any size of business, and even individuals.
Exchange Server does allow you to have an email address from your own domain, but you are limited to one address per license. It also does not permit catchalls.
Exchange Server does however offer very large quotas – 50gb per email account. Licences can also be bundled with other Microsoft business software such as Microsoft Office and Skype for Business.
Exchange Server encrypts your email account using your password as the key. This means no-one can access your email (including Microsoft) at the server. This does not mean however your email cannot be intercepted when sending and receiving , as the encryption is only applied to the email when it’s in your email account. Also, if you download your email, it is only as secure at the device you downloaded it to.
Exchange also does not require a web host or cpanel to run. However if combined with one, you can configure catchalls and many of the other benefits of web hosted email – i.e. you get the large quotas and higher security of Exchange, with the flexibility of Web Hosts.
Conclusion
My advice is to buy a domain and setup a Web Hosted Email Account. The increased level of security, privacy and convenience cannot be overstated – particuarly when you are using your email address to register with large numbers of websites and companies.
Dygiphy has fixed-priced plans for all the services offered here. Contact us to find out more.